GHSA-v4v2-8h88-65qj
Suggest an improvement- Source
- https://github.com/advisories/GHSA-v4v2-8h88-65qj
- Import Source
- https://github.com/github/advisory-database/blob/main/advisories/github-reviewed/2023/11/GHSA-v4v2-8h88-65qj/GHSA-v4v2-8h88-65qj.json
- JSON Data
- https://api.test.osv.dev/v1/vulns/GHSA-v4v2-8h88-65qj
- Aliases
- Related
- Published
- 2023-11-24T16:54:20Z
- Modified
- 2023-12-07T22:59:07Z
- Severity
-
- 6.1 (Medium) CVSS_V3 - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N CVSS Calculator
- Summary
- Attribute Injection leading to XSS(Cross-Site-Scripting)
- Details
-
Summary
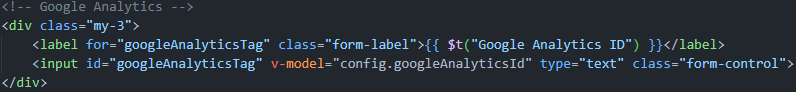
Google Analytics element Attribute Injection leading to XSS
Details
Since the custom status interface can set an independent Google Analytics ID and the template has not been sanitized, there is an attribute injection vulnerability here, which can lead to XSS attacks.
PoC
- Run the latest version of the louislam/uptime-kuma container and initialize the account password.
- Create a new status page.
Edit the status page and change the Google Analytics ID to following payload(it only works for firefox. Any attribute can be injected, but this seems the most intuitive):
123123" onafterscriptexecute=alert(window.name+1),eval(window.name) a="xClick Save and return to the interface. XSS occurs. screenshots:


- Database specific
{ "nvd_published_at": "2023-12-01T22:15:10Z", "github_reviewed_at": "2023-11-24T16:54:20Z", "cwe_ids": [ "CWE-79" ], "severity": "MODERATE", "github_reviewed": true }- References
Affected packages
npm / uptime-kuma
Package
- Name
- uptime-kuma
- View open source insights on deps.dev
- Purl
- pkg:npm/uptime-kuma