A distributed vulnerability database for Open Source
An open, precise, and distributed approach to producing and consuming vulnerability information for open source.
Ecosystems
- AlmaLinux
- 5043 View AlmaLinux vulnerabilities
- Alpaquita
- 10148 View Alpaquita vulnerabilities
- Alpine
- 4248 View Alpine vulnerabilities
- Android
- 2912 View Android vulnerabilities
- Azure Linux
- 12016 View Azure Linux vulnerabilities
- BellSoft Hardened Containers
- 499 View BellSoft Hardened Containers vulnerabilities
- Bitnami
- 8027 View Bitnami vulnerabilities
- Chainguard
- 6851 View Chainguard vulnerabilities
- CleanStart
- 1304 View CleanStart vulnerabilities
- crates.io
- 2445 View crates.io vulnerabilities
- Debian
- 57817 View Debian vulnerabilities
- Echo
- 4057 View Echo vulnerabilities
- GIT
- 88272 View GIT vulnerabilities
- GitHub Actions
- 53 View GitHub Actions vulnerabilities
- Go
- 7064 View Go vulnerabilities
- Hackage
- 32 View Hackage vulnerabilities
- Hex
- 133 View Hex vulnerabilities
- Julia
- 936 View Julia vulnerabilities
- Linux
- 24883 View Linux vulnerabilities
- Mageia
- 5967 View Mageia vulnerabilities
- Maven
- 6536 View Maven vulnerabilities
- MinimOS
- 64993 View MinimOS vulnerabilities
- npm
- 219976 View npm vulnerabilities
- NuGet
- 1713 View NuGet vulnerabilities
- openEuler
- 6930 View openEuler vulnerabilities
- openSUSE
- 12982 View openSUSE vulnerabilities
- OSS-Fuzz
- 3933 View OSS-Fuzz vulnerabilities
- Packagist
- 6399 View Packagist vulnerabilities
- PyPI
- 19995 View PyPI vulnerabilities
- Red Hat
- 20473 View Red Hat vulnerabilities
- Rocky Linux
- 3364 View Rocky Linux vulnerabilities
- Root
- 15495 View Root vulnerabilities
- RubyGems
- 1972 View RubyGems vulnerabilities
- SUSE
- 20644 View SUSE vulnerabilities
- SwiftURL
- 53 View SwiftURL vulnerabilities
- TuxCare
- 5803 View TuxCare vulnerabilities
- Ubuntu
- 55516 View Ubuntu vulnerabilities
- Wolfi
- 4451 View Wolfi vulnerabilities
OSV schema
All advisories in this database use the OpenSSF OSV format, which was developed in collaboration with open source communities.
The OSV schema provides a human and machine readable data format to describe vulnerabilities in a way that precisely maps to open source package versions or commit hashes.
{
"schema_version": "1.7.4",
"id": "GHSA-c3g4-w6cv-6v7h",
"modified": "2022-04-01T13:56:42Z",
"published": "2022-04-01T13:56:42Z",
"aliases": [ "CVE-2022-27651" ],
"summary": "Non-empty default inheritable capabilities for linux container in Buildah",
"details": "A bug was found in Buildah where containers were created ...",
"affected": [
{
"package": {
"ecosystem": "Go",
"name": "github.com/containers/buildah"
},
"ranges": [
{
"type": "SEMVER",
"events": [
{
"introduced": "0"
},
{
"fixed": "1.25.0"
}
]
}
]
}
],
"references": [
{
"type": "WEB",
"url": "https://github.com/containers/buildah/commit/..."
},
{
"type": "PACKAGE",
"url": "https://github.com/containers/buildah"
}
]
}Data sources
This infrastructure serves as an aggregator of vulnerability databases that have adopted the OSV schema, including GitHub Security Advisories, PyPA, RustSec, and Global Security Database, and more.
Use the API
An easy-to-use API is available to query for all known vulnerabilities by either a commit hash, or a package version.
Query by commit hash
curl -d \
'{"commit": "6879efc2c1596d11a6a6ad296f80063b558d5e0f"}' \
"https://api.osv.dev/v1/query"
Query by version number
curl -d \
'{"version": "2.4.1",
"package": {"name": "jinja2", "ecosystem": "PyPI"}}' \
"https://api.osv.dev/v1/query"
Vulnerability Scanner
Install OSV‑Scanner
go install github.com/google/osv-scanner/v2/cmd/osv-scanner@v2
Scan SBOM or Lockfiles
osv-scanner --sbom=cycloned-or-spdx-sbom.json
osv-scanner --lockfile=package-lock.json
Scan directory recursively
osv-scanner -r path/to/your/project
Remediation Tools
Guided Remediation (basic)
osv-scanner fix --non-interactive --strategy=in-place -L path/to/package-lock.json
osv-scanner fix --non-interactive --strategy=relock -M path/to/package.json -L path/to/package-lock.json
Guided Remediation (interactive)
osv-scanner fix -M path/to/package.json -L path/to/package-lock.json
Container Image Scanning
You can use OSV-Scanner to scan your container images for known vulnerabilities.
Scan container image
osv-scanner scan image --serve alpine:3.12

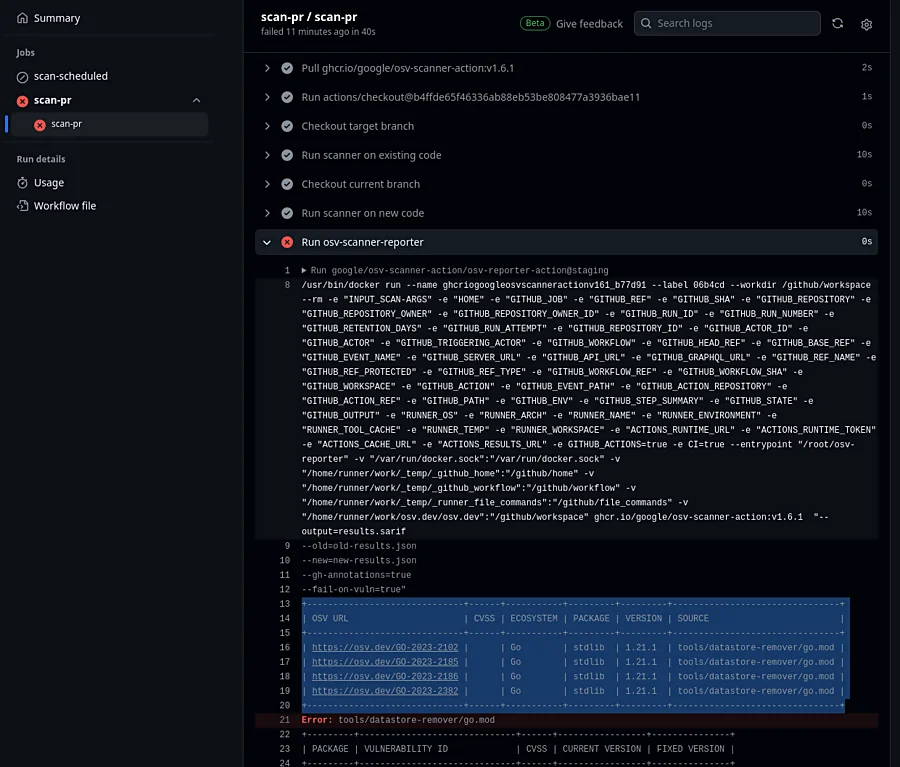
GitHub Workflows
OSV-Scanner also provides reusable GitHub workflows that can be easily integrated into CI/CD pipelines to provide continuous vulnerability scanning coverage. This can scan newly added dependencies in pull requests for introduced vulnerabilities, as well as perform regular vulnerability scans for the entire project.